Part 1 — Configure System
Part 1 will describe how to configure the Jenkins system to add the SonarQube, Keycloak and Gitea servers, and to configure the Kubernetes cloud where our builds are going to run.
SonarQube servers
We add our SonarQube server, so that withSonarQubeEnv can inject the server URL and the authentication token to our build. The name must match the parameter that we pass to the method.

- Environment variables: [ ]
- SonarQube installations:
- Name: sonarqube
- Server URL: https://sonarqube.anrisoftware.com
- Server authN token: xxx
Global Keycloak Settings
Our Jenkins will use Keycloak single sign on (SSO). The documentation of the plugin describes how to configure Keycloak for Jenkins: keycloak-plugin
- Keycloak JSON: { … }
- [ ] Validate Token on each request
- Use default IDP:
Gitea Servers
We are going to use Gitea as our repository. Here we have to configure the Gitea server so that Jenkins can use web-hook triggers.
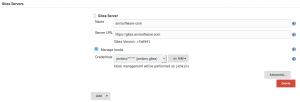
- Gitea Servers
- Name: anrisoftware-com
- Server URL: https://gitea.anrisoftware.com
- [x] Manage hooks
- Credentials: jenkins/**** (jenkins gitea)
Cloud
After we installed Jenkins in Kubernetes, the cloud is already configured with the defaults. The defaults are working, but we are going to use our own Docker image for Maven builds. That is, because we need to able so sign our artifacts with GnuPG. The signatures are necessary if we want to deploy our projects in Maven Central, but it’s also good practice to do so anyway. A signature guarantees that the published artifacts are build from a trusted source.
After we have configured Kubernetes, we can start creating our build pipelines. The builds are then run inside Docker containers. Those container will share a NFS directory that is mounted under /home/jenkins/workspace and we pass all the necessary parameters to sign the created artifacts and to upload the generated reports to a web server via SSH.
Kubernetes
- Name: kubernetes
- Kubernetes URL: https://kubernetes.default
- Kubernetes Namespace: jenkins
- Jenkins URL: http://jenkins:8080
- Jenkins Tunnel: jenkins-agent:50000
Images
Kubernetes Pod Template
- Name: maven-3-jdk‑8
- Namespace: jenkins
- Labels: maven-3-jdk‑8
Containers
Container Template
- Name: jnlp
- Docker image: jenkins/jnlp-slave:3.10 – 1
- Always pull image: [ ]
- Working directory: /home/jenkins
- Command to run:
- Arguments to pass: ${computer.jnlpmac} ${computer.name}
- Allocate pseudo-TTY: [x]
- EnvVars:
Container Template
- Name: maven
- Docker image: erwin82/maven:v3.5.3‑jdk-8‑r.10
- Always pull image: [ ]
- Working directory: /home/jenkins
- Command to run: /bin/sh ‑c
- Arguments to pass: cat
- Allocate pseudo-TTY: [x]
- EnvVars:
EnvVars
Environment Variable
- Key: JENKINS_URL
- Value: http://jenkins:8080
Environment Variable from Secret
- Key: PROJECT_SSH_HOST
- SecretName: jenkins-ssh
- SecretKey: ssh_hosts
Environment Variable
- Key: PROJECT_SSH_HOME
- Value: /root/.ssh
Environment Variable from Secret
- Key: PROJECT_SSH_ID_RSA
- SecretName: jenkins-ssh
- SecretKey: ssh_id_rsa
Environment Variable from Secret
- Key: PROJECT_SSH_USER
- SecretName: jenkins-ssh
- SecretKey: ssh_user
Environment Variable from Secret
- Key: PROJECT_SSH_PASS
- SecretName: jenkins-ssh
- SecretKey: ssh_pass
Environment Variable
- Key: PROJECT_GIT_NAME
- Value: jenkins
Environment Variable
- Key: PROJECT_GIT_EMAIL
- Value: jenkins@anrisoftware.com
Volumes
Persistent Volume Claim
- Claim Name: jenkins-work
- Read Only: [ ]
- Mount path: /home/jenkins/workspace
